Small Retailer
Measurement Framework
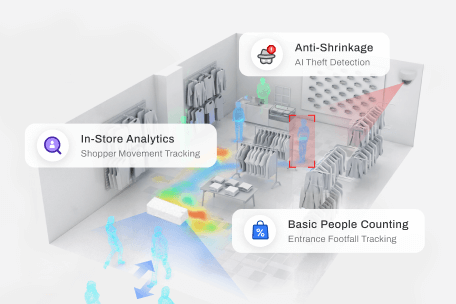
Pro2 measures six operational metrics that describe traffic, behaviour, and engagement. Each metric has a defined measurement method and can be validated through the evaluation workspace to ensure accuracy and consistency across deployments.
Operational Metrics
In / Out Counting
Uses stereo vision to track directional entry and exit events at entrances for accurate traffic and performance analysis.
Outside Traffic
Pedestrian flow measurement at storefront enabling accurate, mathematically sound conversion modelling.
Group Counting
Detects individuals entering together and classifies them as groups using spatial proximity and movement synchronisation.
Visit Duration
Measures time between entry and exit by linking trajectories, enabling analysis of engagement and operational performance.
Staff Exclusion
Identifies and removes staff activity using behaviour, spatial context, and appearance cues to maintain clean customer metrics.
Accuracy & Validation
Pro2 accuracy is measurable, verifiable, and continuously protected. By combining metric depth, environmental resilience, transparent validation, and automated integrity monitoring, Pro2 delivers data that organisations can rely on for operational and strategic decision‑making at scale.
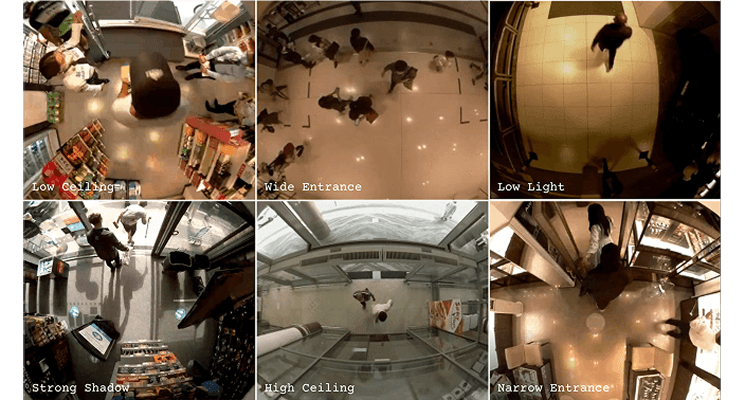
Resilient Across Operational Environments
Pro2 maintains consistent accuracy across diverse, real-world conditions by combining spatial understanding, behavioural analysis, and historical learning.
Reliable performance in:
- Low-light and night environments
- High-density, crowded flows
- Large coverage areas
- Partial occlusion (trolleys, shelving, fixtures)
- Low- and high-ceiling installations
- Semi-outdoor and transitional entrances
Built for industrial environments where conditions are variable and not optimised for analytics.
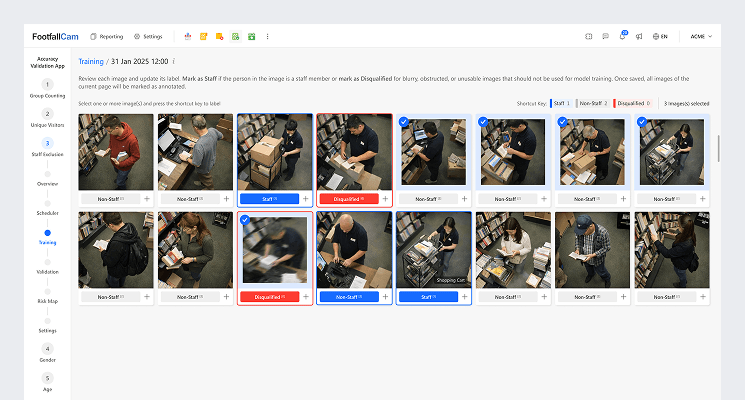
Explainable & Verifiable Accuracy
Pro2 delivers transparent, explainable accuracy through a structured validation workflow, enabling SLA review, contextual analysis, and collaborative assessment.
Validation workspace provides:
- Continuous accuracy visibility
- Trend and variance insights
- Zone- and device-level drill-down
- Evidence for review and discussion
Ensures stakeholders make informed decisions with full visibility, not blind trust.
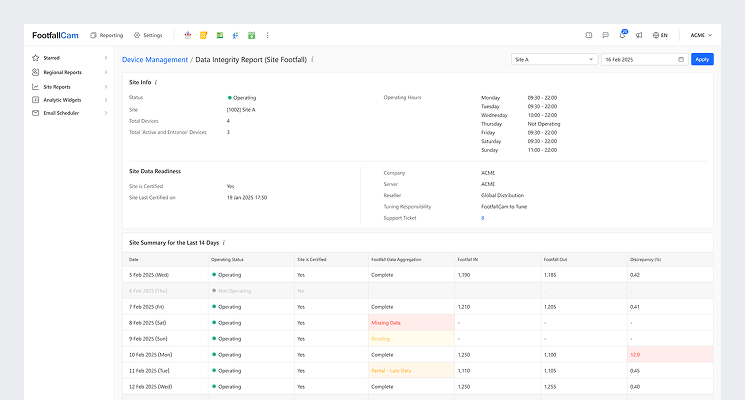
Continuous Accuracy Monitoring & Integrity
Operational metrics are continuously monitored across deployments. Automated checks identify unusual patterns, installation issues, or measurement drift. Alerts guide investigation and corrective actions, ensuring the data remains reliable for operational and strategic decision-making.
Key integrity functions include:
- Accuracy and consistency monitoring across device fleets
- SLA threshold evaluation
- Drift and anomaly detection
- Corrective and mitigation workflows
This ensures that data quality is actively protected throughout the system lifecycle.